Network Port Documentation About 10.139.8.226.8010 and Feedback
This discussion centers on documenting the port 10.139.8.226:8010 with clear endpoint configuration, access controls, and monitoring expectations. It emphasizes auditable labeling, precise references, and interoperability. The goal is a disciplined feedback loop with defined review cadence, issue tracking, and closed-loop validation. Secure practices and least-privilege controls should guide remediation and ongoing accuracy. Stakeholders are invited to weigh governance, timing, and responsibilities to ensure durable documentation integrity, as questions and implications accumulate.
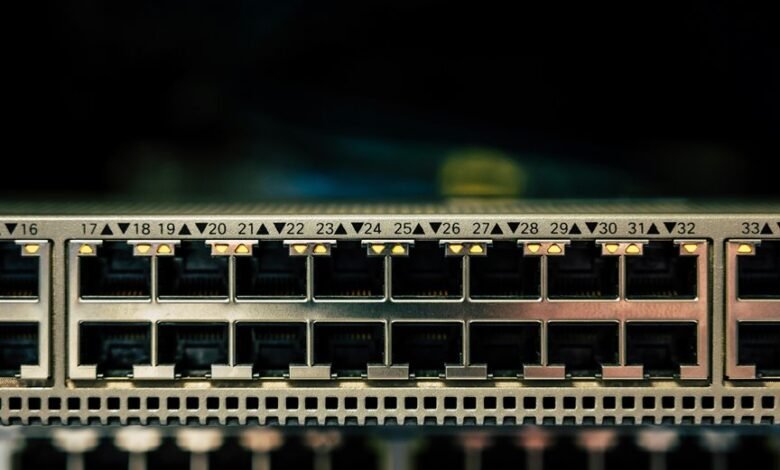
What 10.139.8.226.8010 Port Documentation Means for Your Network
The 10.139.8.226.8010 port documentation represents a specific network endpoint’s configuration and intended usage within an enterprise address space.
It informs networking governance by defining allowable traffic, access controls, and monitoring expectations.
This record supports port security through documented ACLs, rate limits, and logging requirements, enabling disciplined risk management and consistent operational practices while preserving freedom to adapt to evolving infrastructure needs.
How to Read and Label a Port Like 10.139.8.226:8010 for Clarity
Mapping a port label like 10.139.8.226:8010 into concrete governance requires a disciplined reading of its components. The text advocates clear, neutral delineation of address and port, supporting labeling conventions and consistent port naming. Each element is described, enabling precise reference, auditable records, and scalable documentation. This method promotes transparency, interoperability, and freedom to manage networks without ambiguity.
Common Issues and Troubleshooting Paths With 10.139.8.226.8010
Common issues with 10.139.8.226.8010 typically arise from misconfigurations, connectivity constraints, or protocol incompatibilities, requiring a structured diagnostic approach.
The guide outlines repeatable checks: verify port naming conventions, confirm binding and firewall rules, test path MTU, and assess latency. Security considerations include least privilege, auditing, and encrypting sensitive control planes to minimize exposure during remediation.
Collecting Team Feedback to Keep Port Docs Fresh and Accurate
Collecting team feedback is essential to keep port documentation accurate and up to date. The process defines a deliberate cadence for input, reviews, and updates. A formal collaboration cadence ensures diverse perspectives are captured; a closed feedback loop validates changes and prevents drift. Documentation owners institutionalize timely reviews, track issues, and close gaps to maintain clarity, reproducibility, and operational confidence.
Conclusion
The documentation for 10.139.8.226.8010 is an epic, precision-driven blueprint that governs access with surgical clarity and auditable traceability. By labeling the endpoint distinctly, enforcing least-privilege controls, and embedding rigorous monitoring, teams achieve near-mythical risk discipline. Feedback loops, issue tracking, and scheduled reviews transform updates into a disciplined cadence, ensuring resilience. In short, this port’s records become the single source of truth, unassailable and perpetually aligned with secure, interoperable network governance.





